In the ever-evolving digital landscape, ensuring robust network security is crucial for any organisation. Both Azure Firewall and third-party Network Virtual Appliances (NVA) are designed to protect your cloud infrastructure. However, they come with distinct trade-offs in terms of control, responsibility, and scalability. Understanding these differences is essential for informed decision-making.
Common Ground
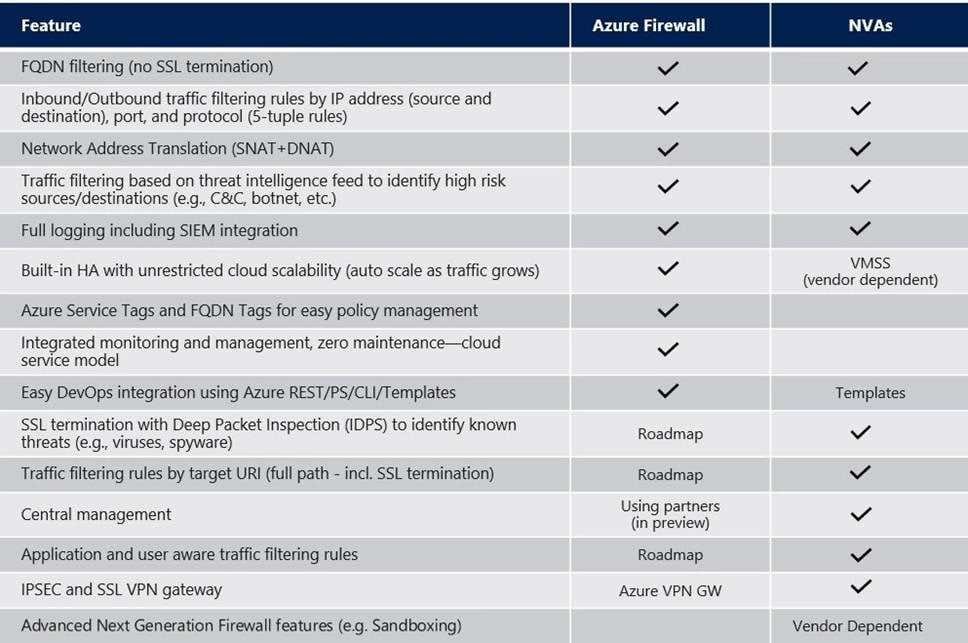
Both Azure Firewall and NVA firewalls share some fundamental capabilities:
- Traffic Inspection: They inspect both north-south and east-west traffic.
- Security Enforcement: They enforce Layer 3 to Layer 7 security rules.
- Central Security Boundary: They act as a central security boundary in hub-and-spoke designs.
Key Differences
- Control
- Azure Firewall:
- Integrated Management: A fully managed service that integrates seamlessly with Azure services, providing a unified management interface through the Azure portal. This allows for straightforward configuration and monitoring.
- Policy Enforcement: Features robust policy enforcement that is easy to implement, enabling efficient management of access rules and application traffic.
- Third-Party NVA Firewalls:
- Customisation: Offer a higher degree of customisation to meet specific security needs or compliance requirements that may not be addressed by Azure Firewall.
- Complex Management: Require more complex management and configuration as standalone services, which may not integrate smoothly with Azure’s ecosystem.
- Responsibility
- Azure Firewall:
- Shared Responsibility Model: Microsoft handles much of the operational responsibility, including maintenance, updates, and scaling, significantly reducing the operational burden on your team.
- Automatic Scaling: Seamlessly scales with your needs, ensuring consistent performance without manual intervention. [Please note that this is not the case when deployed inside of an Azure vWAN]
- Third-Party NVA Firewalls:
- Full Control: Your organisation is responsible for managing updates, scaling, and overall maintenance, potentially increasing operational overhead but allowing greater control over configurations.
- Vendor Dependency: You may become reliant on the vendor for support and updates, introducing complexity if the vendor's service levels do not meet your expectations.
- Scale
- Azure Firewall:
- Dynamic Scaling: Designed to scale dynamically based on your needs, making it ideal for businesses experiencing fluctuating traffic patterns.
- Global Reach: Benefits from Azure’s global infrastructure for quick deployment across various regions.
- Third-Party NVA Firewalls:
- Static Scaling: Scaling is typically more static unless explicitly configured for auto-scaling, limiting flexibility in handling sudden traffic spikes.
- Limited Global Availability: Global deployment may not be as straightforward as with Azure Firewall, complicating multi-region strategies.
Architectural Insights
- Azure Firewall is a fully managed, platform-native solution:
- Microsoft owns availability, scaling, and patching.
- High availability (HA) is built-in and included in the price.
- Does not support VPN or SD-WAN.
- Third-Party NVAs are customer-managed security platforms:
- You are responsible for HA design, scaling, upgrades, and failure management.
- In return, you gain deep inspection capabilities, advanced features, and full control.
- Support for VPN or SD-WAN is available.
High Availability Considerations
- Azure Firewall provides automatic HA without the need for complex clustering or load balancers in its design.
- NVAs, however, require explicit HA architecture involving multiple instances, load balancers, synchronisation, and failover strategies.
Conclusion
When considering Azure Firewall versus third-party NVA firewalls, it’s vital to evaluate your organisation's specific needs for control, responsibility, and scalability. While Azure Firewall excels in ease of management and integration, third-party NVAs offer customisation and advanced control features.
In many mature architectures, organisations effectively use both solutions: Azure Firewall for east-west traffic management and NVAs for north-south traffic flows. Neither choice is inherently right or wrong; rather, they address distinct organisational challenges beyond just technical specifications. By making an informed decision based on these factors, you can enhance your network security posture while aligning with your business goals.